Content
- Criticalstart Announces Enhanced Managed Detection And Response Services Offering For Microsoft Security Suite
- Recommended Resources
- Powerghost
- Washington State Educational Organizations Targeted In Cryptojacking Spree
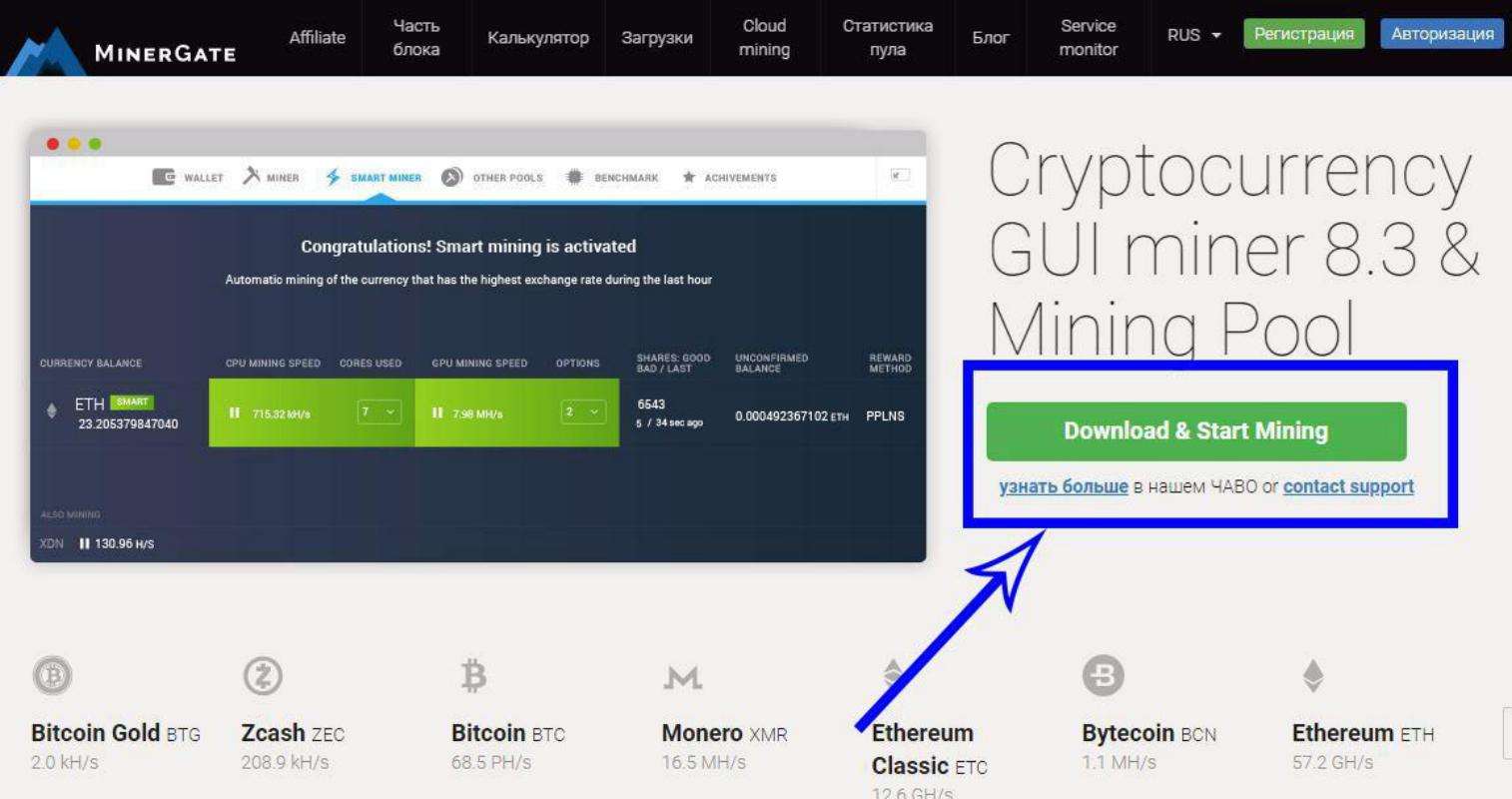
- Minergate Variant Suspends Execution When Victim’s Computer Is In Use
- Mitigating Cryptomining Attacks In Kubernetes

To produce new blocks, cryptocurrencies rely on individuals to provide the computing power. Cryptocurrencies reward people who supply the computing power with cryptocurrency. Those who trade computing resources for currency are called «miners».
- Talk to one of our experts to find out how we can help you protect your website from sophisticated cryptojacking threats.
- PowerShell to execute commands–a PowerShell script injects the malware code into an existing running process.
- In the Cyber threat field, the term ‘mining’ is considered as intensive labor that drains the processing of power and electrical energy.
- The Coinhive case shows just one of the ways cryptojacking can lead to serious damage and data loss.
- Correct prices and promotions are validated at the time your order is placed.
The lure of “easy” money is too tempting for cybercriminals to ignore. And the abundance of tools available makes the bar for entry very low. The study notes that even cybercriminals themselves deal with thefts from their own wallets. «The method is still social engineering with phishing and malware for mining on your hardware. I see names like dusting, and I think about credit card skimming,» Morales said. Continuous security is making continuous threat monitoring and testing an integral part of the continuous integration and continuous delivery (CI/CD) process. The attacker could also create another tmate session from one of the containers . With the reverse shell, the attacker could perform more manual reconnaissance and operations.
Criticalstart Announces Enhanced Managed Detection And Response Services Offering For Microsoft Security Suite
One of the easiest ways to embed a cryptojacking script is within an ad. To make sure it doesn’t happen to you, AdBlocker is a great free extension compatible with numerous browsers. While you do nothing, the crypto-mining malware has been installed in the backend of your computer’s infrastructure via a so-called “script”. Additional malicious images intended to mine cryptocurrency were publicly hosted on Docker Huband downloaded more than two millions times. Cryptojacking can attack any device, any operating system, and can mine any cryptocurrency. Like all pyramid schemes, the ransomware business model works well… for the people on the top. However, the small-time hacker crooks who are looking to make a quick buck have now turned to a new cyberattack method that’s less likely to get stopped by the FBI and is more likely to provide a steady, reliable income.
Lemon Duck Cryptojacking Botnet Changes Up Tactics – Threatpost
Lemon Duck Cryptojacking Botnet Changes Up Tactics.
Posted: Mon, 10 May 2021 07:00:00 GMT [source]
The threat of cryptojacking extends from petty thieves to global crime syndicates. In the event of a compromise, it pays to take the time to understand what happened to help prevent future occurrences. Coalfire director Karl Steinkamp noted that software wallets would only be as strong as their software and security development processes, as well as how the end-user secures it. Cybercriminals now have an easy, profit-generating tool for probing their victim’s defenses. They realized that if a cryptojacking attack goes unnoticed, more extensive exploits surely will too. If they don’t, at least there is a small profit to be made nonetheless. It wasn’t until 2018 that cryptojacking started to attract mainstream attention.
Recommended Resources
JavaScript vulnerabilities are still among the most frequent security compliance violations that enterprises face. A Tala Security report found that 92% of Alexa top 1000 websites provide attackers with sensitive data. It found that 58% of content displayed on customer web browsers comes from third-party JavaScript integrations – the exact types of scripts that CoinHive’s original owners used. The miner who first solves the encrypted problem receives a reward, usually some amount of new cryptocoin. This approach was specially conceived as an incentive for those who sacrifice the time and computing power of their computers to maintain the network and create new coins. Because the complexity of the puzzle calculations has steadily increased over time , miners found that even high-end PCs with a powerful processor could not mine profitably enough to cover the costs involved.
One of the types of Smart Contracts vulnerabilities is integer overflow/underflow.
Find out more about this attack and learn how to protect yourself ????https://t.co/s7WRZujqzV#smartcontract #informationsecurity #cybersecurity #crypto #cryptojacking pic.twitter.com/ScdpQzh5ZD
— ATEITIS (@ateitis_corp) November 29, 2021
Cryptocurrency owners keep their money in virtual “wallets,” which are securely encrypted with private keys. In a transaction, the transfer of funds between the owners of two digital wallets requires that a record of this exchange be entered into the decentralized public digital ledger.
Powerghost
In February, Bad Packets Report found 34,474 sites running Coinhive, the most popular JavaScript miner that is also used for legitimate cryptomining how to prevent cryptojacking activity. In July 2018, Check Point Software Technologies reported that four of the top 10 malware instances it had found were cryptominers.

Before long, people started to look for new ways to mine cryptocurrency, and cryptojacking was born. Instead of paying for an expensive mining computer, hackers infect regular computers and use them as a network to do their bidding.
Continuously monitor resources on your computer such as processing speed and power usage. Installing a performance monitoring app that visualizes the CPU, network, and memory usage of your computer will be very beneficial. Use Trend Micro Cleaner One Pro to help you monitor your computer’s performance. The exponential growth of the cryptocurrency market has attracted not just legitimate investors, but has also presented an option for threat actors to generate revenue through cryptojacking. There’s a new type of cyberattack that is giving cryptocurrency firms nightmares, and it is called Cryptojacking.
Cryptojacking attacks are designed to take advantage of the Proof of Work consensus algorithm used by many blockchains and cryptocurrencies. Proof of Work is designed to decentralize the process of creating blocks to update the blockchain’s distributed ledger. By randomly selecting block creators, the blockchain limits the ability of an attacker to exert too much control over the ledger and rewrite the blockchain’s history. Another type of cryptojacking attack takes place in the cloud, where attackers first steal credentials and then install their scripts into the cloud environment. Some types of cryptocurrency are easier to mine than others, and these are the favorites of hackers.
Washington State Educational Organizations Targeted In Cryptojacking Spree
Special computers collect data from the latest Bitcoin or other cryptocurrency transactions about every 10 minutes and turn them into a mathematical puzzle. Cryptocurrency “clipping” is stealing cryptocurrency in the process of a transaction through the use of malware that automatically substitutes the intended wallet address with the threat actor’s wallet address. After it reached an all-time high in April 2021, new investors desperate not to miss out on the digital gold rush flocked to the exchanges to buy Bitcoin and altcoins. Cryptocurrencies’ current total market cap sits just above $1.7 trillion.
F5 Networks reported this vulnerability in February, and advises rTorrent users to make sure their clients do not accept outside connections. According to the CTA report, Palo Alto Networks has analyzed a variant of the MinerGate malware family and found an interesting feature. This avoids tipping off the victim, who might otherwise notice a drop in performance. In October, Palo Alto Networks released a report describing a cryptojacking botnet with self-spreading capabilities. It spreads by finding Docker Engine deployments that are exposed to the internet without authentication. Palo Alto Networks estimated that Graboid had infected more than 2,000 Docker deployments. During July and August 2018, a cryptojacking attack infected over 200,000 MikroTik routers in Brazil, injecting CoinHive code in a massive amount of web traffic.
Minergate Variant Suspends Execution When Victim’s Computer Is In Use
As you can see, the attacks cybercriminals employ in 2021 to take advantage of the crypto craze are very advanced. We’ve recently seen a few forum threads where threat actors complain about having their virtual currency stolen. One user even held an “ask me anything” session after they lost “100k” due to “being phished” in May 2021. Another wrote, “I want my currency back, this is god damn bad,” after their Etherium was stolen. It’s extremely hard to stop this type of attack once it has started. The fake page hosted on the reverse proxy server will be an exact copy of the real login page; only the URL will be different.
- The infected images were accessed more then two million times, and Palo Alto estimates that the cryptojackers realized $36,000 in ill-gotten gains.
- An alternative method is to use what is known as drive-by crypto mining.
- This makes it all the more difficult to tell if you’re the victim of a cryptojacking script, because there are fewer visible opportunities to detect an intrusion.
- As with other malware kits, cryptojacking as a service can be purchased on the dark web for as little as half a US dollar.
- At the time, it was one of the most common types of malware as cybercriminals exploited the rise in the value of cryptocurrency.
- Since cryptojacking remains chronically underreported, it’s impossible to tell which methods and exploits are the most popular.
Once a victim visits the website or its browser loads the online ad, the cryptomining process is initiated, stealing the resources and profits without the user’s knowledge. One such recently discovered malware, dubbed Hildegard, was found being leveraged by the TeamTNT threat group to target Kubernetes clusters with cryptojacking attacks. In January, researchers also identified an updated malware variant used by the cybercrime gang Rocke Group that targets cloud infrastructures with crypto-jacking attacks. And, in January, researchers dug up new discoveries surrounding a cryptomining operation, called MrbMiner, which was downloading a cryptominer on thousands of internet-facing SQL servers. Cryptojacking first emerged as a major cybersecurity threat in 2018.
To do this, the malware uses resources from the infected computer, such as the processor, graphics card, and main memory, as well as its network bandwidth. The threat of cryptojacking extends from petty thieves to global crime syndicates; in the event of an attack, learning what happened may prevent it from happening again. Compromised systems are used to provide power and compute resources for cryptomining.

’ There are many cloud users in different corners of the world who are totally unaware of the crypto jacking attack. This is the cause due to which organizations are not adopting the security standards that are required to prevent this attack from an occurrence.
In 2021, surging cryptocurrency prices have created new interest in cryptojacking attacks. While the original in-browser cryptojacking script, Coinhive, is no longer in operation, multiple copycat scripts are still active. Additionally, cryptojacking malware targets Internet of Things devices, mobile phones, computers, and routers. Hen reporters asked the infamous bank robber Willie Sutton why he robbed banks he allegedly replied, “because that’s where the money is”. It was only a matter of time that cybercriminals, specifically, ransomware extortioners, started to target their currency of choice, Bitcoin, as a means of gaining wealth. If Willie Sutton was living today, he would probably be a cryptojacker in cyberspace, launching cryptojacking attacks and cryptomining assaults on cryptocurrency firms. Another widespread method is to inject a malicious mining script into a legitimate website or block of online ads that run on many websites.
One of the types of Smart Contracts vulnerabilities is integer overflow/underflow.
Find out more about this attack and learn how to protect yourself ????https://t.co/s7WRZujqzV#smartcontract #informationsecurity #cybersecurity #crypto #cryptojacking pic.twitter.com/ScdpQzh5ZD
— ATEITIS (@ateitis_corp) November 29, 2021
They created a code which could be embedded in every website to mine Monero. This cryptocurrency doesn’t require any specialized hardware to be mined – an average PC is enough. See, Coinhive had this innovative idea of using the CPU’s power of a website visitor to mine cryptocurrency and therefore make ads obsolete. That’s the really short version of how cryptocurrency works, ladies and gentlemen. Even if they fail to contain an illegal cryptominer, you can just reboot the device into safe mode and uninstall the malicious app. To be blunt – it’s an effortless way for cybercriminals to make money.
The other method is to inject a script on a website or an ad that is delivered to multiple websites. Once victims visit the website or the infected ad pops up in their browsers, the script automatically executes. Whichever method is used, the code runs complex mathematical problems on the victims’ computers and sends the results to a server that the hacker controls. The consequences of a cryptojacking attack may be limited to decreased performance, but don’t get too complacent. Cybercriminals looking to find a way to maintain a steady profit are turning into cryptojacking. Although the effects of cryptojacking may seem harmless, users should still be wary. Any cyberthreat that uses your computer’s resources should be a concern because it affects your business and productivity.
A free or older service that was great at launch may no longer receive updates as often as you need them. If your browser supports blocking individual websites, you can keep a running list of no-go websites. You can typically add suspicious URLs to an index via the browser’s security or general settings. This will have many short-term consequences, including damage to internal hardware and erratic behavior (errors, slowdowns, etc.). It leads to further wear on components, which is often a root cause of reduced performance over time.
Can mining be detected?
Cryptocurrency mining can be detected in the network. Machine learning can be employed to detect mining services automatically. Dedicated web application collects IP addresses and service availability of various mining pool servers.
Slow performance hurts business productivity, system crashes and downtime cost sales and reputation, and expensive high-performance servers become expensive poorly-performing servers. And of course, operational costs spike as corporate resources are directed away from their intended uses to serve the needs of cryptominers. Cryptojacking attacks are common because it’s a safe method for hackers to gain access to your resources.
They target a number of personal computers – like yours – to build a distributed network, rather than build a large-scale cryptomining enterprise, which requires a lot of space, hardware, power, and supervision. The risk of being caught and identified is also much less than with ransomware.
First of all – if a cybercriminal messed with a website’s scripts, it’s the owners who should detect it. Facebook and Starbucks’s WiFi mined cryptocurrency as well, thanks to the malicious Coinhive script. This program accepts different parameters that control configuration settings of the running miner such as username, password, CPU usage, priority, threads, and algorithm names respectively.
- This example only illustrates what happens to Google Chrome browsers but this doesn’t mean that other browsers are immune to threats.
- The improved AWS feature allows users to trigger Lambda functions from an SQS queue.
- To understand the mechanics of the threat and how to protect yourself against it, let’s begin with a bit of background.
- While individual phones have relatively limited processing power, when attacks occur in large numbers, they provide enough collective strength to justify the cryptojackers’ efforts.
- Normally, a person mining Bitcoin would pay for their computer and their own electricity bill and hope to break even.
Deploy a true next-generation endpoint protection platform .Organizations must be prepared to prevent and detect all threats, including known and unknown malware, as well as identifying in-memory attacks. This requires a solution that includes next-gen AV protection, as well as endpoint detection and response , to prevent attacks and gain full visibility throughout the environment. The scripts might also check to see if the device is already infected by competing cryptomining malware. A cryptominer might also have a kill prevention mechanism that executes every few minutes, as the AT&T Alien Lab post notes. The intent of the code is not to harm the host, rather hijack its CPU resources in order to launch attacks on other computer systems particularly cryptocurrency targets.
Author: Felipe Erazo


